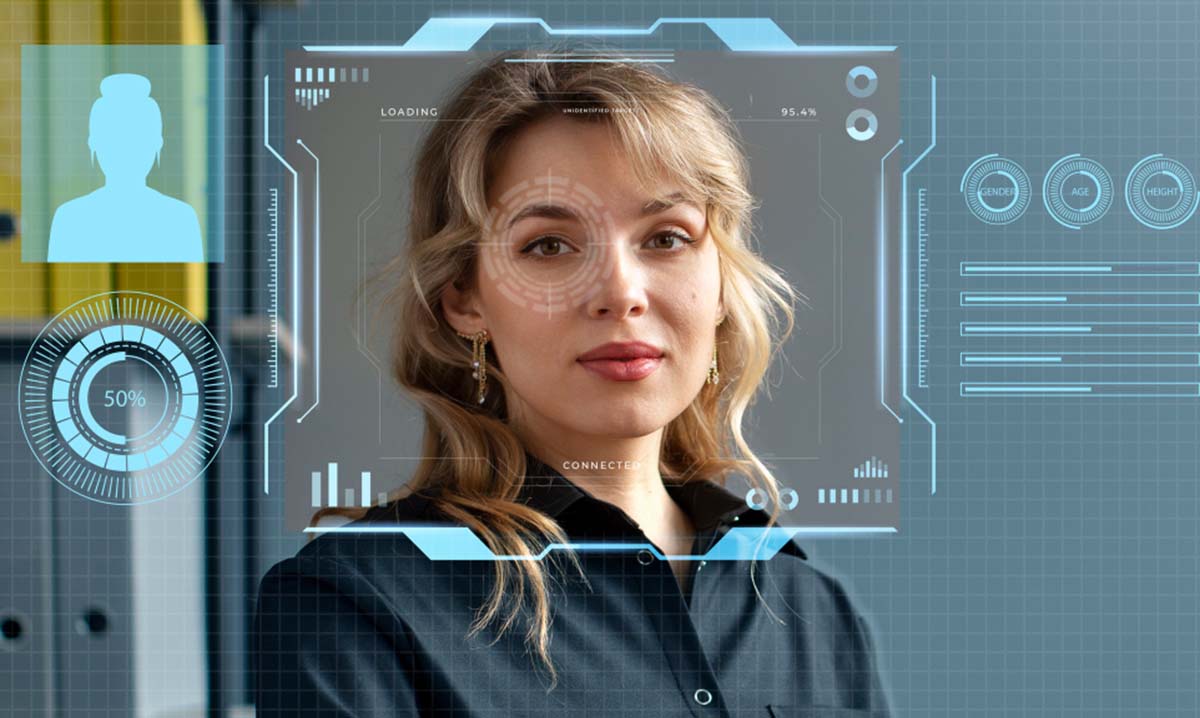
Deepfakes have moved from novelty to business risk. Federal agencies and standards bodies now treat synthetic audio, video, and image manipulation as a real fraud and trust problem. The FTC has warned that voice cloning can be used to impersonate real people, while NIST has documented that deepfakes can support deception at scale and that many detection methods still have limits in everyday deployment.
Executives are high-value targets because their names, faces, and voices carry authority. A fake CEO video, a cloned voicemail from a founder, or an impersonated social profile can push employees, investors, customers, or reporters into acting before they verify what they saw.
What makes executive deepfakes so risky?
- They borrow credibility that already exists.
- They spread fast across social platforms, chat apps, and email.
- They can support fraud, extortion, stock manipulation, or reputational harm.
- They often work because people respond to urgency and status before they pause to verify.
A sensible defense starts before an incident
- Build a short list of executives most likely to be impersonated.
- Audit public exposure: speeches, podcasts, earnings calls, interviews, and social clips all provide source material for voice and video spoofing.
- Set internal verification rules for payment requests, media statements, and sensitive approvals.
- Use callback verification and shared phrases for urgent requests.
- This is also where digital risk protection becomes useful, since it helps organizations spot warning signs before fake content gains traction. CISA has specifically advised organizations to use rolling passphrases to defend against virtual impersonation attempts.
What strong protection looks like in practice
- Protection should cover open-web monitoring, social impersonation, fraud domains, leaked credentials, and escalation workflows, not just alerts in a dashboard.
- Include dark web and leak-site monitoring for exposed credentials and personal data tied to executives. CISA recommends credential monitoring services that watch the dark web for compromised credentials.
- Use 24/7 digital sentinel services for high-risk leaders and key events such as product launches, earnings calls, mergers, or public controversies, when impersonation attempts are more likely.
- Build clear ownership across security, legal, communications, and executive support teams so no one is guessing during a crisis.
The reputational side of the problem
- Deepfake attacks are not only security incidents. They can also damage trust with customers, investors, partners, and employees.
- Strong brand reputation safeguarding means having a plan to address false content quickly, explain the facts clearly, and keep confusion from spreading.
- In many cases, the public response matters almost as much as the technical response, especially when a fake video or audio clip begins circulating widely.

Steps to take in the first 24 hours
- Confirm whether the audio, video, or account is fake.
- Capture evidence before the post disappears or changes.
- Alert legal, security, communications, and executive staff at the same time.
- Notify employees if the content could trigger phishing, payment fraud, or media confusion.
- Begin rapid content removal once the material is verified, using preserved URLs, screenshots, timestamps, and account details.
- Report relevant scams to the FTC and IC3 and notify affected partners or customers when impersonation may reach them.
Why monitoring alone is not enough
- Detection tools help, but synthetic-content detection and provenance methods are still maturing and may be years away from broad deployment on common devices.
- That means companies should not rely on “the software will catch it” as their only line of defense.
- A better model combines monitoring, human review, clear escalation, and policy-based verification for sensitive actions.
- It also helps to keep a proactive digital risk takedown process in place so repeat uploads, cloned accounts, and spoofed sites are tracked and addressed over time.
Also Read: Why Does Brand Monitoring Matter and How Does It Benefit Your Business?
Frequently Asked Questions
1. How does a digital risk takedown service work for deepfake videos?
A takedown service usually verifies the fake, preserves evidence, identifies where it is hosted, and files platform, legal, or abuse complaints based on impersonation, fraud, trademark, copyright, or terms-of-service violations. Speed matters because reposts and mirrored accounts can multiply quickly.
2. What is the best way to monitor the dark web for executive data leaks?
The best approach combines credential monitoring, breach intelligence, and reviews of leak sites, forums, and criminal marketplaces. CISA recommends monitoring for compromised credentials, while FTC guidance on stolen data underscores the need to act quickly when exposed personal information appears for sale.
3. Can AI monitoring services detect voice cloning attempts in real-time?
Some vendors claim real-time detection, and the FTC has encouraged research in this area. Still, NIST has warned that many synthetic-content detection methods are not fully proven at scale. Real-time alerts can help, but human verification remains essential for high-stakes decisions.
4. How can Digital Risk Protection (DRP) prevent CEO fraud?
DRP lowers the odds of CEO fraud by spotting spoof domains, fake social accounts, leaked credentials, and impersonation campaigns early. That only works when it is paired with callback verification, employee training, email authentication, and strict approval controls for payments or sensitive disclosures.
5. What are the legal steps for removing AI-impersonated brand content?
The legal path depends on the platform and the facts. Companies often start by preserving evidence, then filing impersonation and fraud reports, and, where applicable, trademark or copyright complaints. The FTC’s impersonation rule gives regulators stronger tools against business impersonation, but company counsel should guide the response.
Protect your executives before a deepfake turns into a costly crisis. Connect with 24ieye to strengthen your digital risk defense with continuous monitoring, fast response, and expert-led takedown support.